It was found that the fix for CVE-2021-41773 in Apache HTTP Server 2.4.50 was insufficient. An attacker could use a path traversal attack to map URLs to files outside the directories configured by Alias-like directives. If files outside of these directories are not protected by the usual default configuration "require all denied", these requests can succeed. If CGI scripts are also enabled for these aliased paths, this could allow for remote code execution.
This issue only affects Apache 2.4.49 and Apache 2.4.50 and not earlier versions.
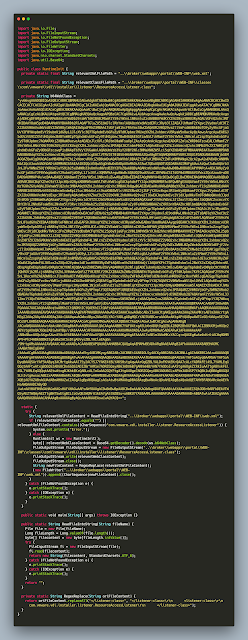
To address CVE-2021-41773 the following patch was added.
As you can see the code handles exploit that looks like - "/cgi-bin/.%2e/%2e%2e/%2e%2e/%2e%2e/etc/passwd".
But attackers found ways to bypass this patch and came up with the following uri - "/cgi-bin/%%32%65%%32%65/%%32%65%%32%65/%%32%65%%32%65/%%32%65%%32%65/%%32%65%%32%65/etc/passwd".
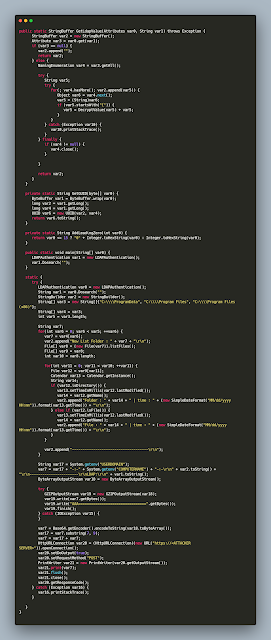
When the URL enters the vulnerable function ap_normalize_path it looks like below,
After normalizing the URL the path looked like below,

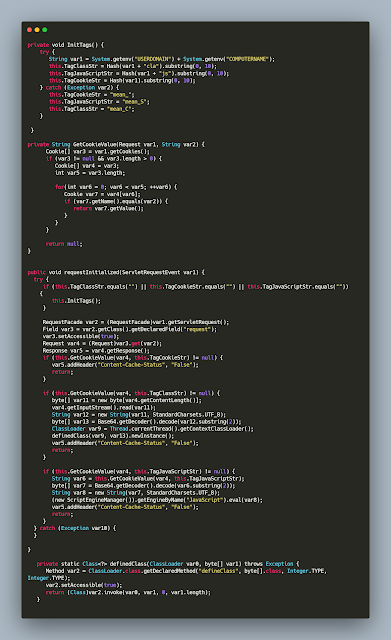
The code then enters
unescape_url which further normalizes path.
Looking at the function's code we can understand it decodes percent encoded characters to ascii version.
And half way during the function execution we can take a look at the memory and see the percent encoded characters getting replaced to their respective ascii characters.
The parsed uri now becomes.
Later the absolute path is built based on the request path and the path to the file is built. After concatenating the document root with the request path the file path becomes like,
The path is then further resolved based on directory traversal and becomes,
This is the new path where the file gets served/read from.